Bonus Abuse in iGaming: How It Works and How to Stop It (2026)

Mari Dimasi
Content & Growth
In late 2025, a gambling fraud analyst shared a case study that captures the economics perfectly. A single bonus abuse ring had created over 1,200 accounts across three sportsbooks in six months. Each account claimed a welcome bonus worth $50-200. The ring’s total take was over $180,000, and the operators had no idea until a pattern review caught velocity anomalies in their withdrawal data.
That operation was small by industry standards. Sumsub’s 2025 iGaming fraud report found that bonus abuse accounts for 63.8% of all fraud in online gambling, making it the single largest fraud category. Between 2022 and 2023, betting platforms lost $1.2 billion to incentive abuse alone. An inexperienced abuser makes up to $20,000 per month. A skilled one operating at scale extracts up to $600,000.
For every dollar an operator spends acquiring a genuine new player, a portion goes straight to fraudsters who will never place a real bet. Here is how bonus abuse works, why it is so hard to stop, and what actually prevents it.
How bonus abuse works
The mechanics are straightforward, which is part of what makes the problem so widespread. Any platform offering per-user promotional incentives is a target.
The welcome bonus cycle
A fraudster creates Account A with a stolen identity and a fresh email address. They claim the $100 welcome bonus, meet the minimum wagering requirements using low-risk betting strategies (backing both sides of a low-margin market), and withdraw $80 in profit. Then they create Account B with a different identity and repeat.
Each cycle takes 30 minutes to a few hours depending on the wagering requirements. With automation tools handling the repetitive parts (account creation, form filling, bet placement), a single operator can run dozens of cycles per day.
Free bet extraction
Free bets are even more exploitable. The fraudster claims a “Bet $10, Get $50 in Free Bets” promotion on each fake account. They place the qualifying bet, receive the free bets, and use them on high-odds selections. Free bets return only the profit (not the stake), so the expected value is roughly 70% of the free bet amount. On a $50 free bet, that is $35 per account with minimal risk.
At 100 accounts, that is $3,500 from a single promotion. Major sportsbooks run these promotions continuously around sporting events, giving abusers a steady pipeline of extraction opportunities.
Deposit match abuse
Deposit match bonuses (100% match up to $500) require more capital but yield higher returns. The fraudster deposits $500, receives $500 in bonus funds, meets the wagering requirements, and withdraws the profit. Sophisticated abusers use matched betting techniques: placing opposing bets on two accounts to guarantee a return while converting the bonus funds into withdrawable cash.
Organized bonus rings
The most damaging operations are organized. A ring of 10-20 people, or a single operator using device farms, systematically harvests promotions across every major platform. The February 2026 FanDuel indictment revealed exactly this model: two men used 3,000 stolen identities to create thousands of fake accounts, claimed promotional bonus bets on each one, and transferred winnings to personal bank accounts through virtual stored-value cards. Their total take over five years: $3 million.
Why bonus abuse is so expensive for operators
The direct cost of bonus abuse is the promotional spend that goes to fraudsters instead of genuine new players. But the downstream damage is much larger.
Wasted acquisition spend
Marketing teams measure customer acquisition cost (CAC) as total promotional spend divided by new depositing players. When 15% of “new players” are fraudsters claiming bonuses, the real CAC is 15% higher than reported. Budget allocation decisions based on inflated acquisition numbers lead to overspending on channels and promotions that attract abusers rather than genuine players.
Distorted lifetime value
Bonus abusers have a lifetime value of negative whatever the bonus cost. They are not going to become regular players. They deposit the minimum, extract the bonus, and never return. When these accounts pollute LTV calculations, the entire retention strategy is built on wrong numbers.
Chargeback costs
Some bonus abusers go further: they extract the bonus, then dispute the original deposit as unauthorized. The operator loses the bonus, the deposit, and pays a chargeback fee. Each $100 chargeback costs approximately $207 when processing fees, penalties, and administrative costs are included.
Regulatory exposure
Regulators view systematic bonus abuse as an indicator of weak AML and identity verification controls. The UKGC’s 2025 penalties framework allows fines of up to 15% of gross gambling yield for serious breaches. In the first half of 2025, the global casino industry paid $160.3 million in regulatory fines. Operators who cannot demonstrate robust fraud detection face increasing enforcement risk.
Why standard defenses fail against bonus abuse
Operators have tried everything, and the smart abusers have adapted to each defense.
KYC and identity verification
KYC tells you the name on the account. It does not tell you whether the same person controls 50 other accounts under different names. Sumsub reports that 76% of fraud attempts occur after KYC is completed because fraudsters use identities that pass verification.
Stolen identities are cheap: the FanDuel fraudsters bought personal data of 3,000 victims on the darknet. Synthetic identities combine real fragments (a valid SSN, a genuine address) with fabricated details. Deepfake technology now passes selfie-based liveness checks, with deepfake fraud growing 700% year-over-year between Q1 2024 and Q1 2025.
IP address monitoring
Flagging accounts from the same IP catches only beginners. Residential proxy services route traffic through genuine home internet connections for a few dollars per gigabyte. Anti-detect browsers like Multilogin assign a different proxy to each browser profile, so every account appears to connect from a different city.
An estimated 1.75 billion people use VPNs worldwide, making IP-based signals unreliable as a primary detection method.
Email and phone verification
Disposable email services generate unlimited addresses for free. Virtual phone numbers provide SMS verification for a few cents per number. These are not barriers. They are minor line items in a bonus abuser’s operating budget.
Wagering requirements
Increasing wagering requirements makes bonuses less attractive to legitimate players and barely slows down abusers. Professional bonus abusers use mathematical techniques (dutching, arbing, low-margin market exploitation) to meet wagering requirements with minimal loss. The result: operators lose genuine players to unattractive promotions while abusers continue operating at slightly lower margins.
Bonus limits and caps
Reducing bonus amounts or capping promotional periods limits the damage per account but does not prevent multi-accounting. A $25 bonus claimed 500 times is $12,500, the same problem at a different scale. The abuser simply creates more accounts to compensate.
What actually stops bonus abuse
Effective bonus abuse prevention targets the one thing fraudsters cannot easily change: the physical device.
Device fingerprinting at registration
Device fingerprinting collects 70+ signals from every visitor’s hardware and browser: GPU renderer, canvas rendering, audio processing, WebGL output, installed fonts, screen properties, and more. These signals combine into a persistent identifier that survives cookie clears, incognito mode, and browser switches.
When a bonus abuser creates their second account on the same laptop and browser, the device fingerprint matches the first account. By the tenth account, the pattern is unmistakable. No identity change, VPN switch, or email address can mask the underlying hardware. Even if a browser update generates a new fingerprint, the platform retains historical identifiers per account, so the link between past and future accounts on the same machine can still be established.
Anti-detect browser detection
Anti-detect browsers are the bonus abuser’s primary tool for spoofing device fingerprints. Over 24 products exist in the market, including Multilogin (2,800+ enterprise customers), GoLogin (500,000+ users), and Dolphin Anty. They work by randomizing the browser parameters that standard fingerprinting collects.
Advanced device intelligence detects these tools by identifying inconsistencies between claimed and actual hardware. A browser profile claiming to be Chrome on macOS but rendering WebGL with a Windows GPU driver is a spoofing attempt. Guardian’s browser tampering detection catches these mismatches.
Velocity monitoring
Device-level velocity tracking counts how many accounts, deposits, bonus claims, and withdrawals originate from a single device over time. Legitimate players create one account. Bonus abusers create many. Setting velocity thresholds at the device level (not the IP level) catches abuse patterns that network-based monitoring misses entirely.
Cross-platform device sharing
Forward-thinking operators are beginning to explore shared device intelligence across platforms. When a device flagged for bonus abuse on Platform A appears on Platform B, the second platform can apply enhanced scrutiny before paying out. This network effect makes it progressively harder for abusers to find unexploited targets.
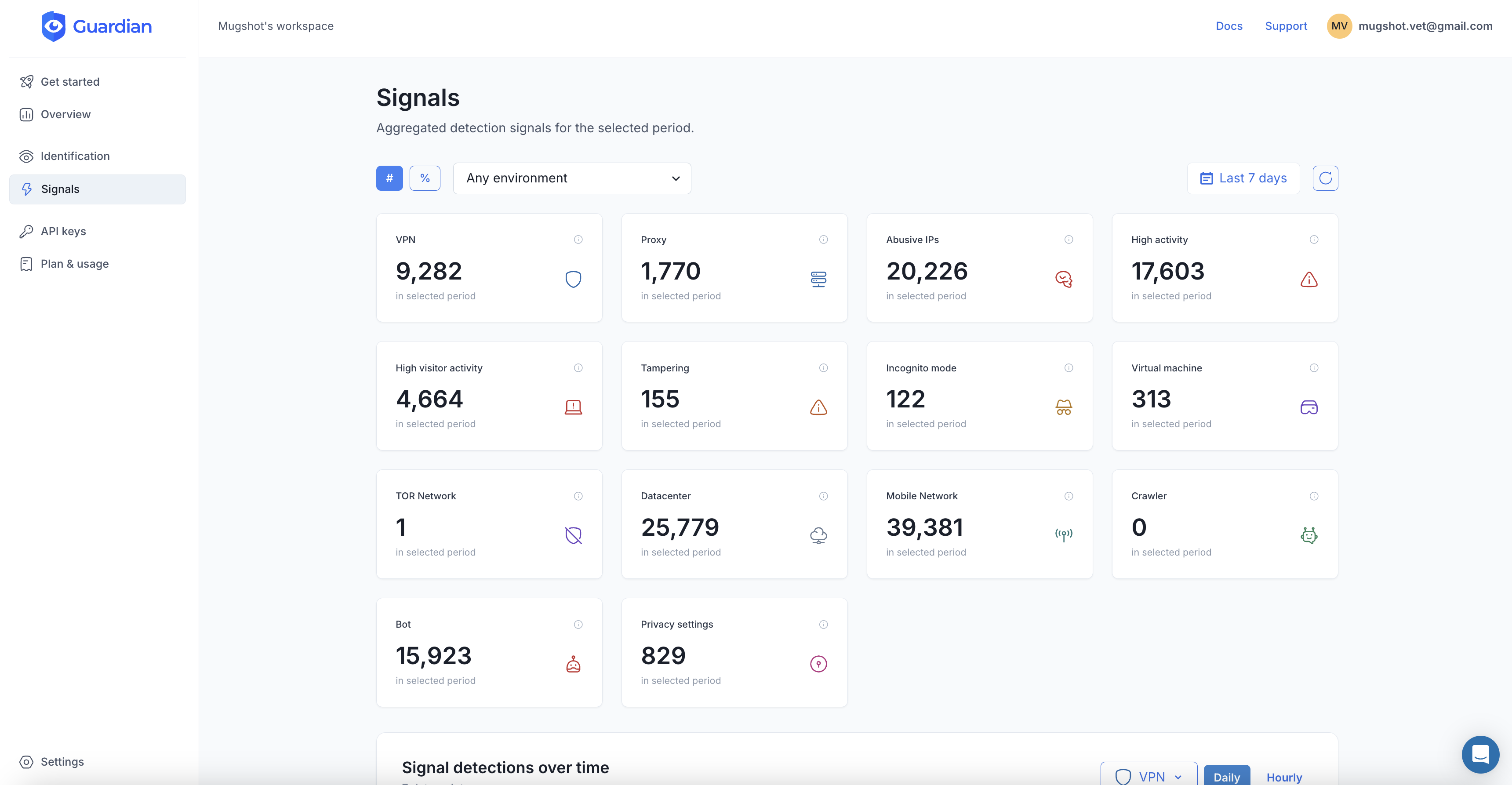
Detecting bonus abuse with Guardian
Guardian’s device intelligence provides the signals needed to catch bonus abuse at the account creation stage, before any promotional funds are disbursed.
Integration at the bonus claim point
// Client-side: collect device signals when user claims a bonus
import { loadAgent } from '@guardianstack/guardian-js';
const guardian = await loadAgent({
siteKey: 'YOUR_SITE_KEY',
});
const { requestId } = await guardian.get();
// Send requestId to your server with the bonus claim request// Server-side: check device history before approving the bonus
import {
createGuardianClient,
isTampering,
isVPN,
} from '@guardianstack/guardianjs-server';
const client = createGuardianClient({
secret: process.env.GUARDIAN_SECRET_KEY,
});
const event = await client.getEvent(requestId);
const { visitorId } = event;
// Check if this device has claimed bonuses on other accounts
const previousClaims = await db.query(
'SELECT account_id, bonus_type FROM bonus_claims WHERE visitor_id = $1',
[visitorId]
);
if (previousClaims.length > 0) {
// Same device, different account - block the bonus
await denyBonus(accountId, 'multi_account_device');
await flagForReview(visitorId, previousClaims);
}
// Also check for anti-detect browser usage
if (isTampering(event)) {
await denyBonus(accountId, 'browser_tampering');
}Risk scoring for bonus decisions
Not every flagged signal is fraud. A shared household computer, a device upgrade, or a legitimate VPN user might trigger false positives. Guardian’s signals support risk scoring rather than binary blocking:
- Low risk: New device, no tampering, no VPN, no velocity anomalies. Approve the bonus automatically.
- Medium risk: VPN detected or moderate velocity (2-3 accounts on the same device). Approve but monitor withdrawal behavior.
- High risk: Browser tampering detected, high velocity (5+ accounts), or residential proxy usage. Block the bonus and flag for manual review.
- Critical: Known multi-accounting device (10+ linked accounts). Block registration entirely.
A practical implementation plan
Rolling out bonus abuse detection does not require rebuilding your entire platform. Start with these steps.
-
Instrument the registration flow. Add Guardian’s JavaScript agent to your signup page. Store the
visitorIdwith every new account. This takes hours, not weeks. -
Build a device-to-account lookup. Create a database mapping
visitorIdtoaccount_id. Query this mapping on every new registration and every bonus claim. -
Set initial velocity thresholds. Start conservative: flag any device linked to more than 2 accounts for manual review. Adjust thresholds based on your false positive rate and abuse patterns.
-
Monitor bonus claim patterns. Track which promotions are most targeted, what times of day abuse peaks, and which device characteristics correlate with fraud. Sumsub data shows most fraudulent activity happens between 4-8 a.m., while legitimate registrations peak around 6 p.m.
-
Layer with existing KYC. Device intelligence works alongside your existing identity verification. KYC satisfies regulatory requirements. Device signals catch the fraud that KYC misses.
-
Report to compliance. Maintaining records of detected and prevented bonus abuse strengthens your regulatory position. Demonstrate to the UKGC, MGA, or Curacao Gaming Authority that you actively detect and prevent multi-accounting.
The bottom line
Bonus abuse is not a cost of doing business. It is a solvable problem. The operators who treat promotional fraud as inevitable are subsidizing an industry of professional abusers while penalizing their genuine players with weaker promotions and higher wagering requirements.
Device intelligence shifts the balance. When every bonus claim is tied to a physical device, multi-accounting stops being profitable. The economics that make bonus abuse attractive (low risk, high reward, easy to scale) collapse when the abuser’s device betrays them on the second attempt.
Start your free trial to protect your promotional budgets from bonus abuse.
Frequently asked questions
What is bonus abuse in online gambling?
How much does bonus abuse cost gambling operators?
How do bonus abusers create multiple accounts?
Can device fingerprinting stop bonus abuse?
What is the difference between bonus abuse and matched betting?
What regulations require operators to prevent bonus abuse?
Related articles

· 13 min read
Multi-Accounting in Online Gambling: How to Detect and Stop It
Multi-accounting costs gambling operators billions yearly. Learn how fraudsters exploit fake accounts and how device intelligence stops them.

· 13 min read
Click Farm Fraud: How to Detect and Stop Fake Traffic (2026)
Click farms drain ad budgets, pollute analytics, and fake engagement. Learn how to detect and block them with device intelligence.

· 13 min read
Device Farm Fraud: How to Detect and Shut Down Fake Traffic
Device farms power fake accounts, promotion abuse, and credential stuffing at scale. Learn how device intelligence detects and stops them.