Click Farm Fraud: How to Detect and Stop Fake Traffic (2026)

Piero Bassa
Founder & CEO

In 2025, the global cost of click fraud hit $104 billion, up from $88 billion the year before. That same year, Thai police raided two houses in Sa Kaeo province and found 474 iPhones, 347,200 SIM cards, and three operators paid $14,700 a month to generate fake engagement. That single operation was one of thousands running worldwide.
Click farm fraud is not a niche problem. It is an industry. For every $3 your business spends on digital marketing, roughly $1 is lost to ad fraud. And click farms, operations purpose-built to generate fake human-like engagement at scale, are one of the hardest forms to catch.
Here is how click farms work, why most defenses miss them, and what actually stops them.
What click farm fraud actually looks like
Click farm fraud is organized fake engagement. The “farm” part is literal: rows of devices, racks of phones, or clusters of virtual machines, all generating clicks, installs, views, or likes that look real but are not.
Physical device farms
The simplest version is a room full of smartphones. Operators, usually low-paid workers in developing countries, manually tap through ads, install apps, create accounts, and leave reviews. A single worker can operate 20-50 phones simultaneously using custom racks and automated scripts that handle the repetitive parts.
The Thailand operation is a textbook example: hundreds of iPhones connected to cheap local SIM cards, run from rented houses. Similar operations have been documented in China, India, Bangladesh, and Kenya. The economics are straightforward. Paying a worker $2-5 per hour to generate thousands of fake clicks is far cheaper than the advertising revenue those clicks steal.
Virtual device farms
More sophisticated operations skip physical hardware entirely. They spin up hundreds of virtual machines or Android emulators, each configured with different screen resolutions, browser versions, and device profiles. Anti-detect browsers like Multilogin or GoLogin let a single operator manage dozens of browser profiles that each appear as a unique device.
Virtual farms scale faster and cost less per fake click than physical operations. They can run 24/7 without human workers and generate engagement volumes that no room full of phones could match.
Hybrid operations
The most dangerous click farms combine both approaches. Human workers handle actions that require human-like behavior (navigating pages, pausing between clicks, varying session times), while automation handles the volume. This hybrid approach produces traffic that is nearly indistinguishable from real users when examined one session at a time.
The real cost of click farm fraud
The damage goes beyond wasted ad spend. Click farms corrupt the data you use to make business decisions.
Direct budget drain
Advertisers lose an average of 22% of their budgets to fraudulent clicks. Small businesses are hit hardest, with some losing up to 30% of their ad spend to non-human traffic. Across all platforms, 14-22% of paid search clicks are estimated to be fraudulent or invalid, depending on the industry and geography.
For a business spending $50,000 per month on paid search, that means $7,000-$11,000 going to clicks that will never convert. Over a year, that is $84,000-$132,000 in wasted spend.
Analytics corruption
Every fake click pollutes your data. Click farm traffic inflates impressions, skews click-through rates, and creates phantom engagement that makes campaigns look better than they are. When your analytics show 10,000 clicks but only 100 conversions, you cannot tell whether your landing page is broken or whether 9,000 of those clicks were fake.
This leads to bad decisions. Teams optimize campaigns based on corrupted signals, allocate budgets toward channels that are inflated by fraud, and kill campaigns that were actually performing well with real users.
Downstream business damage
When click farms target affiliate programs, they steal commission payments for conversions that never happened. Affiliate fraud accounted for 17% of all affiliate traffic in 2022, costing companies $3.4 billion. When they target competitors’ ads, they drain budgets without generating any value. When they inflate app install numbers, they distort user acquisition metrics and LTV calculations that inform product and investment decisions.
How click farms evade detection
Click farms invest heavily in looking legitimate. Here are the specific techniques they use and why each one works.
Device rotation
Physical farms cycle through different phones, tablets, and browsers. Each device has a genuinely unique hardware profile: different screen resolution, different GPU, different set of installed fonts. This means each click comes from what appears to be a distinct user. A farm with 500 phones can simulate 500 unique visitors per rotation cycle.
IP rotation through residential proxies
Click farms route traffic through residential proxy networks that assign real household IP addresses. These IPs belong to actual ISP customers, often unknowingly enrolled through free VPN apps, compromised routers, or bandwidth-sharing SDKs. Because the IPs are genuine residential addresses, they pass geo-verification checks and IP reputation lookups that would flag datacenter traffic instantly.
A single proxy provider can offer access to millions of residential IPs across hundreds of countries. The farm switches IPs every few minutes, making it impossible to correlate activity based on network data alone.
Behavioral mimicry
Advanced click farms program their bots and train their workers to mimic real user behavior. They scroll pages before clicking. They vary session duration between 30 seconds and several minutes. They visit multiple pages per session. They move the mouse in natural curves rather than jumping straight to the click target.
Some operations use AI-driven tools that learn behavioral patterns from real user sessions and replay them with slight variations. The result is traffic that passes basic behavioral checks because it genuinely looks human at the individual session level.
Anti-fingerprinting tools
Virtual farms use anti-detect browsers that spoof device fingerprints. These tools override the browser’s reported screen size, WebGL renderer, canvas output, font list, and dozens of other signals. Each browser profile presents a completely different fingerprint to websites, making it appear as though each session comes from a different machine.
Tools like Multilogin, GoLogin, and Dolphin Anty have legitimate uses for marketers managing multiple accounts. But they are also standard equipment in click farm operations because they defeat naive fingerprinting implementations.
Account rotation
Farms create and cycle through thousands of fake accounts. They use disposable email addresses, temporary phone numbers for SMS verification, and CAPTCHA-solving services to get past signup barriers. Each account is used for a limited number of actions before being retired, preventing any single account from accumulating enough suspicious activity to trigger alerts.
Why traditional defenses fail
Most ad fraud detection relies on signals that click farms can easily manipulate.
IP blocking is useless when farms rotate through millions of residential IPs. Block one address and the next click arrives from a completely different household in a different city. You cannot block residential IPs aggressively without cutting off real customers.
User-agent filtering catches only the laziest scripts. Any competent farm spoofs its user agent to match current versions of Chrome, Safari, or Firefox. This takes one line of configuration.
CAPTCHAs barely slow farms down. Human-operated farms solve them naturally because real people are doing the clicking. Bot-operated farms use solving services that cost $1-3 per 1,000 challenges and return results in seconds. AI models now solve most CAPTCHA types at 96%+ accuracy.
Platform-level detection helps but is not sufficient. Google’s invalid click detection catches an estimated 40-60% of fraudulent clicks. That sounds reasonable until you realize the remaining 40-60% still costs advertisers roughly $35 billion annually on Google’s platforms alone. Platform detection is optimized to minimize false positives (wrongly blocking real clicks), which means it lets sophisticated fraud through.
Basic rate limiting fails against distributed operations. When 500 devices each generate a small number of clicks, no single device exceeds any threshold. The fraud is visible only when you look at the operation as a whole, not at individual sessions.
How to detect click farm fraud
Catching click farms requires looking at signals they cannot easily fake. The key insight is that while farms can change surface-level attributes (IPs, cookies, user agents), they cannot change the underlying hardware and behavioral patterns that connect their sessions.
Device fingerprinting
Device fingerprinting collects dozens of signals from each visitor’s browser and hardware: canvas rendering, WebGL output, audio processing characteristics, installed fonts, screen properties, and more. Combined, these signals create a persistent identifier for each device.
A click farm with 500 phones has 500 fingerprints. When those same 500 devices generate 50,000 clicks across your campaigns, fingerprinting reveals that the “50,000 unique users” are actually 500 recycled devices. This is the signal that IP rotation and cookie clearing cannot hide.
Advanced fingerprinting persists across incognito mode, cookie clears, and VPN changes because it reads hardware-level attributes that the operator cannot modify without physically swapping the device.
Behavioral clustering
Individual click farm sessions may look human. But when you analyze patterns across sessions, the coordination becomes visible. Look for:
- Timing clusters. Dozens of “unique” users clicking the same ad within seconds of each other, especially at odd hours in the reported timezone.
- Session uniformity. Real users show wide variance in session duration, page depth, and interaction patterns. Farm traffic tends toward tighter distributions because the same scripts or instructions drive every session.
- Geographic impossibility. Ten devices with different IPs but identical hardware fingerprints appearing in ten different countries within an hour.
VPN and proxy detection
Farms rely on proxies to mask their true location. Detecting proxy and VPN usage strips away this layer of concealment. When a device claims to be in New York but its traffic routes through a known proxy network, that mismatch is a strong signal.
Combine proxy detection with device fingerprinting and you get the full picture: the same device, hiding behind rotating IPs, clicking your ads from apparently different locations.
Velocity and clustering signals
Track engagement velocity per device fingerprint, not just per IP or per account. Metrics that reveal farms:
- Clicks per device per hour. A real user might click 2-3 ads in a browsing session. A farm device cycles through dozens.
- Unique IPs per device. A real user might show 1-3 IPs per day (home, office, mobile). A farm device routing through proxies might show 50+.
- Account density per device. If 20 different user accounts have logged in from the same device fingerprint, that device is being shared in ways that real users do not.
Click-to-conversion analysis
Click farms generate clicks, not customers. Track the conversion rate per device fingerprint over time. Legitimate traffic clusters around your normal conversion rate with natural variance. Farm traffic shows near-zero conversions because the clicks are not driven by purchase intent.
When a device fingerprint has generated 200 clicks across your campaigns with zero conversions, zero add-to-carts, and zero meaningful page engagement, you have strong evidence of fraud regardless of how human the individual clicks appeared.
Stopping click farms with device intelligence
Detecting click farm fraud requires combining multiple signals into a single decision. Device intelligence platforms do this by analyzing every visitor at the hardware level and surfacing the signals that farms cannot fake.
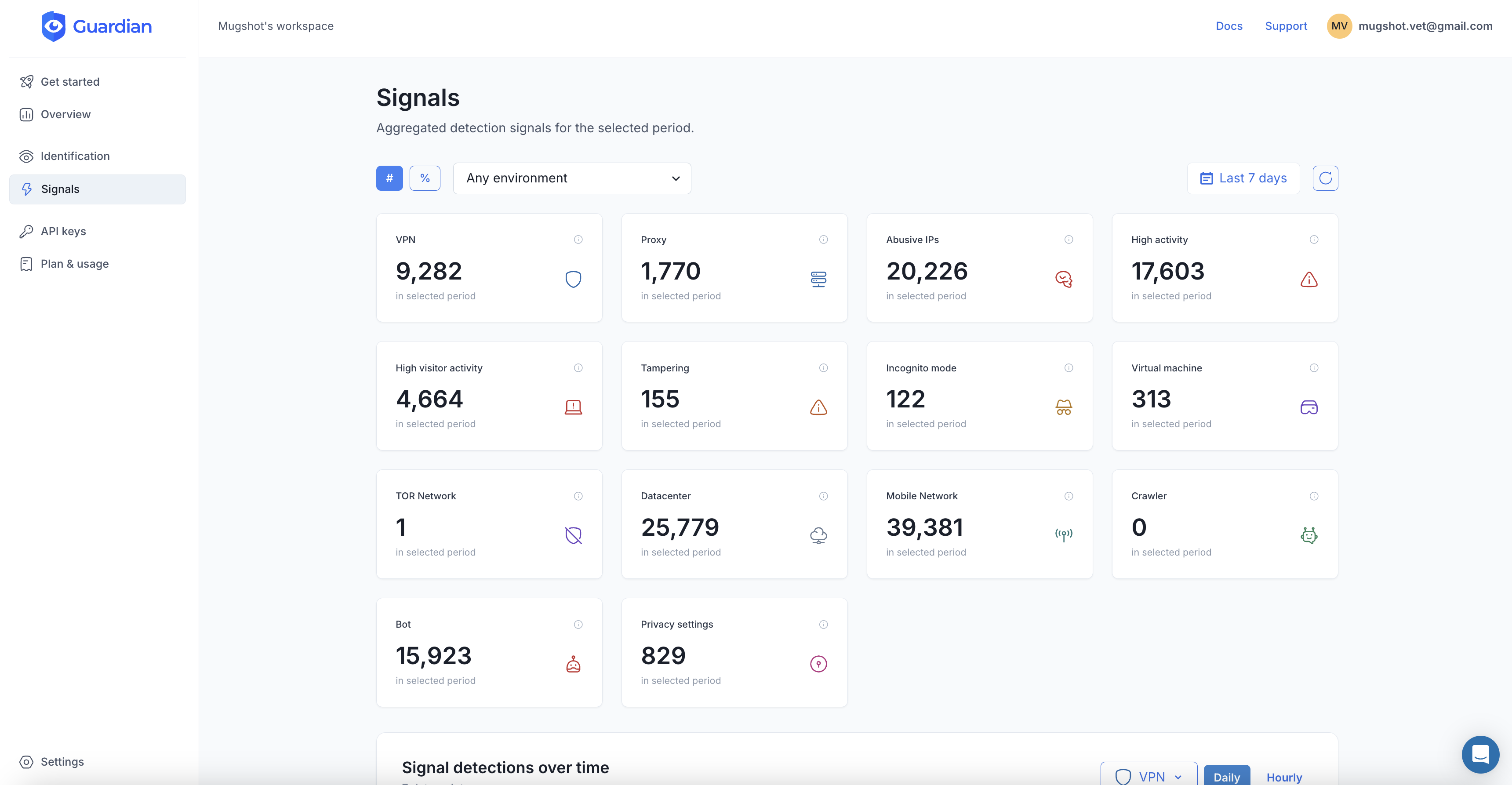
Guardian collects 70+ browser and device signals from each visitor, generates a persistent visitor ID that survives cookie clears and IP changes, and returns real-time detection signals you can act on immediately.
How it works in practice
Add the client-side agent to your pages:
import { loadAgent } from "@guardianstack/guardian-js";
const guardian = await loadAgent({ siteKey: "YOUR_SITE_KEY" });
const { requestId } = await guardian.get();On your server, retrieve the full analysis before crediting a click or conversion:
import { createGuardianClient, isBot, isVPN }
from "@guardianstack/guardianjs-server";
const client = createGuardianClient({
secret: process.env.GUARDIAN_SECRET_KEY,
});
const event = await client.getEvent(requestId);
// Check for click farm signals
const isSuspicious = isBot(event)
|| isVPN(event)
|| event.products.identification.data.browserTampering.value
|| event.products.identification.data.velocity.events5m > 20;The response includes:
- Bot detection that identifies automated browsers, headless Chrome, Selenium, Playwright, and other automation tools that farms use to scale beyond human operators.
- VPN and proxy detection that flags residential proxies, datacenter traffic, and Tor exit nodes. This catches the IP rotation layer that farms depend on.
- Browser tampering detection that identifies anti-detect browsers spoofing their fingerprint. When a browser reports being Chrome on Windows but its canvas and WebGL output match a different configuration, that mismatch is detected.
- Velocity signals that track how many requests, IPs, and accounts a single device has generated over the last 5 minutes, 1 hour, and 24 hours. Farms produce velocity patterns that no real user would.
- Persistent visitor ID that links all sessions from the same device, even across cookie clears, incognito mode, and VPN switching. This is what connects the dots across hundreds of seemingly unrelated farm clicks.
Layering signals for confidence
No single signal is conclusive. A real user might occasionally use a VPN. A shared family device might show multiple accounts. The power of device intelligence is in combining signals:
- A device using a VPN, with browser tampering detected, and 50 clicks in the last hour is almost certainly part of a farm.
- A device with a clean fingerprint, no VPN, and 2 clicks in a day is almost certainly a real user.
- A device with high velocity but no other red flags might warrant monitoring rather than blocking.
This layered approach lets you block fraud aggressively while keeping false positives near zero.
Building a click farm defense strategy
Deploying device intelligence is the foundation. But a complete defense strategy also requires process.
1. Establish baselines first. Before blocking anything, collect data. Run device intelligence on your traffic for a week to understand your normal patterns: typical velocity per device, VPN usage rates, browser tampering frequency. This baseline tells you what “normal” looks like for your audience.
2. Start with monitoring, not blocking. Flag suspicious traffic and review it manually before automating enforcement. This catches edge cases and helps you set thresholds that match your risk tolerance.
3. Layer your signals. Combine device intelligence with click-to-conversion analysis, geographic plausibility checks, and engagement depth metrics. Each layer catches a different subset of farm activity.
4. Automate at the threshold. Once you trust your signal combinations, automate: block clicks from confirmed bot devices, flag VPN traffic for review, and suppress billing for sessions that match farm patterns.
5. Review and adapt. Click farms evolve. Monitor your detection rates monthly. Track which signals catch the most fraud. Adjust thresholds when you see new evasion patterns. The farms will adapt, and your defenses need to adapt faster.
Click farm fraud is not going away. The economics are too favorable for attackers. But with device-level intelligence, you can see through the rotation, the proxies, and the mimicry to identify the machines behind the fraud, and cut them off before they drain another dollar.
Frequently asked questions
What is click farm fraud?
How much does click fraud cost advertisers?
How do click farms avoid detection?
Can Google detect click farm fraud?
What is the difference between click farms and click bots?
How does device fingerprinting detect click farm fraud?
Related articles

· 13 min read
Device Farm Fraud: How to Detect and Shut Down Fake Traffic
Device farms power fake accounts, promotion abuse, and credential stuffing at scale. Learn how device intelligence detects and stops them.
· 11 min read
E-Commerce Fraud Prevention at Scale: What Actually Works
57% of e-commerce traffic is bots. Platform-level fraud prevention sounds great in theory. Here is what actually works at scale.

· 11 min read
Bonus Abuse in iGaming: How It Works and How to Stop It (2026)
Bonus abuse accounts for 63.8% of iGaming fraud. Learn how fraudsters exploit promotions and how device intelligence detects them before they cash out.