Device Farm Fraud: How to Detect and Shut Down Fake Traffic

Domenico Lorenti
Cloud Architect

In 2024, fraud investigators at a major food delivery platform discovered a single bad actor who had accessed 400 different accounts on one device. In 30 days, that device consumed thousands of dollars in new-user promotions. A separate case exposed a ring of 18 people running over 2,000 stolen identities to create fake driver accounts, netting nearly $800,000 over two years.
Both operations relied on the same infrastructure: device farms. These are not edge cases. Fake accounts now represent 57% of driver-side fraud on gig economy platforms, and 75% of fraud professionals rank application tampering (including device farming) as their top concern heading into 2026.
Here is how device farms work, why standard defenses fail, and how device intelligence shuts them down.
What a device farm actually is
A device farm is exactly what it sounds like: a collection of devices operated together to commit fraud at scale. The “farm” can take several forms.
Physical device farms
The simplest version is a rack of smartphones. Dozens or hundreds of phones, often older models bought in bulk, sit in custom shelving with USB hubs for power and charging. Operators cycle through each device: create an account, claim a promotion, reset the phone, repeat. A single operator can manage 50-100 phones using automation tools that handle the repetitive taps and swipes.
These setups are cheap to build. A rack of 100 used Android phones costs under $2,000. At scale, the return from promotion abuse, fake account bonuses, or referral fraud far exceeds the hardware investment.
Emulator farms
More sophisticated operations skip physical hardware entirely. Android emulators like BlueStacks, Nox, or custom builds let a single server run dozens of virtual devices simultaneously. Each emulator instance can be configured with different screen sizes, device models, and Android versions to appear as a unique phone.
Emulator farms scale faster and cost less than physical farms. A $500/month cloud server can run 50+ emulator instances, each creating accounts, claiming bonuses, or generating fake engagement around the clock.
Virtual machine clusters
At the web application level, attackers use virtual machines and anti-detect browsers to create hundreds of unique browser profiles. Tools like Multilogin, GoLogin, and Dolphin Anty let a single operator manage dozens of browser sessions, each with a spoofed fingerprint, separate cookies, and different proxy connections.
These setups target web-based platforms: e-commerce promotions, SaaS free trials, referral programs, and ad campaigns.
Hybrid operations
The most dangerous farms combine all three. Physical devices handle actions that require real hardware (app installs, SMS verification), emulators handle volume tasks (account creation, engagement farming), and human operators step in for anything that requires CAPTCHA solving or human-like decision making.
What device farms are used for
Device farms enable fraud at a scale that no individual account could achieve.
Promotion and bonus abuse
Every platform that offers per-user incentives, sign-up bonuses, referral credits, first-order discounts, free trials, is a target. A device farm with 500 devices can claim 500 bonuses. One documented case showed a single fraudster creating 800 fake accounts to exploit new-user coupons, stealing 1.5% of the platform’s total redeemed coupon value in a single month.
In online gaming and gambling, bonus abuse accounts for 50% of all fraud cases. Device farms systematically create accounts to claim welcome bonuses, free bets, and loyalty rewards, then cash out or transfer the value.
Fake account creation
Gig economy platforms are heavily targeted. Fraudsters create fake driver and courier accounts using stolen or synthetic identities, verified through the device farm’s SIM cards and phone numbers. These accounts are then rented to unqualified drivers, used to exploit incentive programs, or sold on secondary markets.
A 2024 investigation exposed 18 people operating over 2,000 fake driver accounts across ride-sharing and delivery platforms, earning nearly $800,000 before being caught.
Credential stuffing at scale
Device farms run credential stuffing campaigns across hundreds of devices simultaneously. Each device tests stolen username/password pairs against a different target, staying under per-device rate limits. With 15 billion compromised credentials circulating publicly, the farm just needs a 0.1% hit rate to compromise thousands of accounts.
Review manipulation and engagement fraud
Fake reviews, fake app installs, fake likes, and fake followers are all device farm products. Each device creates an account, posts a review, and moves to the next target. Because each review comes from a different device with a genuinely different hardware fingerprint, platforms struggle to connect the activity to a single operation.
Ad fraud
Device farms generate fake clicks and impressions across advertising platforms. Physical device farms are particularly effective because the clicks come from real devices with real hardware fingerprints, making them harder to detect than bot-generated clicks.
Why standard defenses fail
Most fraud prevention starts with network-level signals. Against device farms, these signals are nearly useless.
IP blocking sees nothing
Device farms route traffic through residential proxies that assign real household IP addresses to each device. A farm with 100 devices can appear to be 100 users in 100 different cities. Blocking one IP does nothing because the next request comes from a completely different address. And blocking residential IPs aggressively means blocking real customers.
Rate limiting misses distributed attacks
Per-IP rate limiting triggers when a single address sends too many requests. But a device farm distributes activity across hundreds of devices and IPs. Each device stays well under any threshold. The fraud is only visible when you look at the operation as a whole, and IP-based rate limiting cannot do that.
CAPTCHAs are irrelevant
Physical device farms use real human operators who solve CAPTCHAs naturally. Emulator farms use solving services that cost $1-3 per 1,000 challenges. AI models now solve most CAPTCHA types at 96%+ accuracy. CAPTCHAs add friction for real users without meaningfully slowing device farm operations.
Basic device IDs are not enough
86% of platforms use some form of device identification. But only 48% use tamper detection, and only 52% use location intelligence. That gap is exactly what device farms exploit. A device ID that does not detect emulators, virtual machines, or anti-detect browsers misses the core infrastructure that farms rely on.
Signals that expose device farm activity
Device farms leave patterns that surface-level checks miss but hardware-level analysis reveals.
Repeated device attributes across accounts
When 50 “unique users” all have the same GPU renderer string, the same audio processing fingerprint, and the same WebGL output, they are the same device. Physical farms cycle devices across accounts, but the hardware fingerprint stays constant. Device fingerprinting catches this reuse even when cookies are cleared and IPs rotate between sessions.
Emulator and virtual machine signatures
Emulators leave distinct traces. Their GPU renderer strings reference virtual hardware (e.g., “Android Emulator” or “SwiftShader”). Audio stack processing differs from physical devices. Screen resolution ratios may not match any real phone model. Battery status APIs return default values. These signals are difficult to spoof because they come from the virtualization layer itself, not from software that the operator can configure.
Browser tampering indicators
Anti-detect browsers override fingerprint signals: canvas output, WebGL renderer, font lists, and more. But spoofed values create internal inconsistencies. A browser that claims to be Chrome on Windows but produces canvas output consistent with Safari on macOS has been tampered with. The gap between reported and actual values is the detection signal.
Velocity anomalies
Real users have natural engagement patterns. They browse, idle, and interact at varying speeds. Device farms optimize for throughput. They produce tight clusters of sign-ups, rapid sequences of promotion claims, and high-volume activity at unusual hours. Velocity measured per device fingerprint (not per IP) reveals this pattern even when the farm distributes across many network addresses.
Network infrastructure patterns
Farms route through shared infrastructure: datacenter IPs, known proxy providers, VPN endpoints, and hosting providers. When a device fingerprint shows genuine mobile hardware but connects from a datacenter IP, that mismatch signals a farm using cloud-based proxies.
How device intelligence detects device farms
Stopping device farms requires looking at the machine, not the network. Device intelligence analyzes the hardware behind every request and surfaces the signals that farms cannot fake.
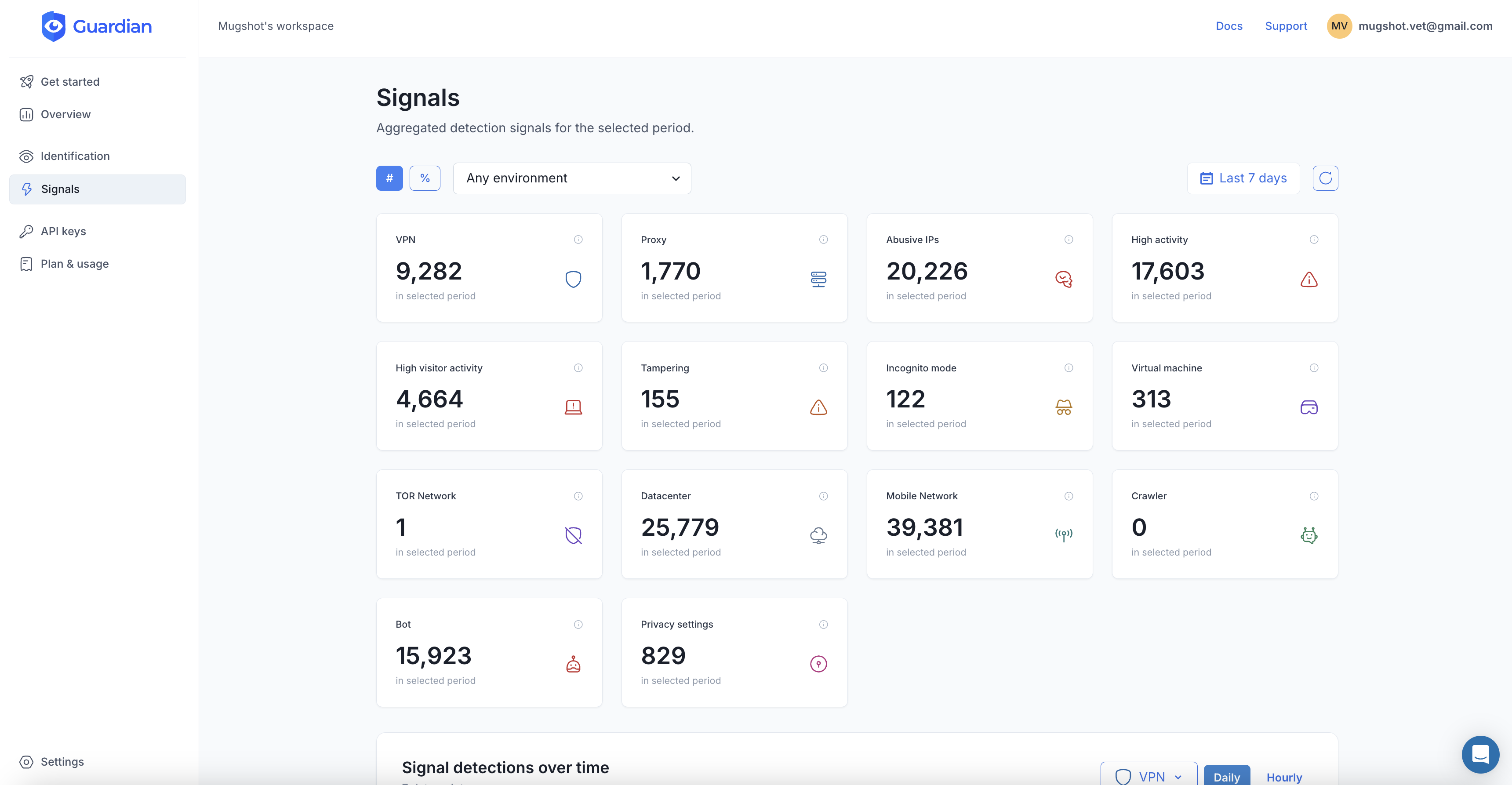
Guardian collects over 100 browser and device signals from each visitor, generates a persistent visitor ID tied to the physical device, and returns real-time detection data you can act on immediately.
Implementation
Add the client-side agent to capture device signals during critical actions (sign-ups, logins, promotions, payments):
import { loadAgent } from "@guardianstack/guardian-js";
const guardian = await loadAgent({ siteKey: "YOUR_SITE_KEY" });
const { requestId } = await guardian.get();
// Send requestId to your backend with the form submissionOn your server, retrieve the full device analysis:
import {
createGuardianClient,
isBot,
isVPN,
isTampering,
isVirtualized,
} from "@guardianstack/guardianjs-server";
const client = createGuardianClient({
secret: process.env.GUARDIAN_SECRET_KEY,
});
const event = await client.getEvent(requestId);What the response tells you
Each Guardian event returns layered detection signals built for catching device farms:
Persistent visitor ID. A stable identifier tied to the physical device hardware. It persists across cookie clears, incognito mode, browser updates, and IP changes. When a device farm cycles the same phone through 50 accounts, all 50 share the same visitor ID. Query your database, and the pattern is immediately visible.
Bot detection. Identifies automation tools (Selenium, Puppeteer, Playwright) and headless browsers that farms use to script repetitive actions. Returns a boolean detected flag plus a 0-100 automation probability score. Scores above 80 warrant blocking. Scores between 40-80 suggest adding friction.
Virtualization detection. Flags emulators and virtual machines with a confidence score. Catches BlueStacks, Nox, and custom Android emulators that farms use to simulate hundreds of devices from a single server. The detection reads hardware-level signatures that emulator configuration tools cannot override.
Browser tampering detection. Identifies anti-detect browsers and fingerprint spoofing. Returns an anomaly score (0-1) and specific indicators: vendor_mismatch, canvas_spoofing, webgl_anomalies. When an anti-detect browser claims to be one device but produces signals consistent with another, the mismatch is flagged.
VPN and proxy detection. Flags VPN, proxy, Tor, and datacenter traffic. Includes timezone analysis: the timezoneDifference field shows the gap between the browser’s reported timezone and the IP’s geographic timezone. A device claiming to be in New York but routing through a proxy in Singapore produces a timezone mismatch that real users rarely show.
IP intelligence. Classifies the connecting IP as residential, datacenter, hosting provider, or known abuser. Includes an abuser_score for IPs with fraud history. Device farms using cloud-hosted proxies are flagged by the datacenter classification even when the IP itself has no abuse history.
Velocity signals. Tracks request volume per IP and per visitor ID across rolling windows: 5 minutes, 1 hour, 24 hours, and 7 days. High-risk thresholds: more than 10 requests per visitor in 5 minutes, or more than 60 per hour. Farms that stay under per-IP limits are caught by per-visitor velocity because the same hardware generates the requests regardless of which proxy it routes through.
Making fraud decisions
Combine signals to build graduated responses:
const { visitorId } = event.products.identification.data;
const bot = isBot(event);
const vpn = isVPN(event);
const tampered = isTampering(event);
const virtualized = isVirtualized(event);
const velocity5m = event.products.velocity.data.visitorVelocity["5m"];
// Check how many accounts this device has created
const priorAccounts = await db.accounts.count({
where: { visitorId }
});
// High risk: block
if (bot || tampered || virtualized) {
return deny("Device blocked due to automation signals");
}
// Device reuse: block promotion
if (priorAccounts >= 1) {
return deny("Promotion limited to one per device");
}
// Medium risk: challenge
if (vpn || velocity5m > 10) {
return requireVerification("Additional verification required");
}
// Low risk: allow
return allow();This approach catches the core device farm patterns:
- Same device, multiple accounts caught by visitor ID lookup
- Emulator or VM caught by virtualization detection
- Anti-detect browser caught by tampering detection
- Automated scripts caught by bot detection
- Proxy routing caught by VPN/IP intelligence
- High-throughput activity caught by velocity signals
Protecting specific use cases
Promotion and referral fraud
The most common device farm target. For every sign-up, check whether the visitor ID has previously claimed the promotion. A single database query replaces fragile cookie or email-based deduplication. Referral fraud is caught by comparing the visitor IDs of the referrer and the new user. If they match, it is a self-referral.
For more implementation detail, see new account fraud prevention.
Account takeover
Device farms run credential stuffing at scale by distributing login attempts across many devices. Per-visitor velocity signals catch this: a single device attempting logins across multiple accounts triggers high-velocity alerts regardless of IP rotation. See account takeover prevention for the full implementation pattern.
Free trial abuse
SaaS platforms offering free trials are systematically exploited by device farms creating accounts, using the trial, resetting the device, and repeating. Visitor ID persistence breaks this cycle. Even after a device reset, the fingerprint links the new account to the previous trial usage.
Payment fraud
Device farms test stolen card numbers across hundreds of sessions. Each transaction appears to come from a different user. Visitor ID reveals the same device behind all attempts. Combined with bot detection and velocity signals, this catches payment fraud patterns before chargebacks hit.
Building a device farm defense
1. Instrument critical flows. Add device intelligence to sign-up, login, promotion claim, and payment flows. These are the entry points that farms target.
2. Store visitor IDs with every account. This is the foundation. When every account is linked to a device fingerprint, spotting multi-accounting is a simple database query instead of a statistical analysis.
3. Start with monitoring. Run device intelligence in observation mode for a week before enforcing blocks. Establish baselines for normal velocity, VPN usage, and device diversity in your user base.
4. Layer signals, do not rely on one. A VPN alone is not fraud. A VPN plus virtualization plus high velocity plus multiple accounts from the same visitor ID is a device farm. Combine signals for confident decisions.
5. Graduate your responses. Block confirmed automation (bots, emulators). Challenge suspicious patterns (VPN plus velocity). Allow clean traffic. This keeps false positives low while catching coordinated abuse.
6. Review and adapt. Device farms evolve their techniques. Monitor which signals catch the most fraud, adjust velocity thresholds as your user base grows, and watch for new emulator or spoofing tools that may require detection updates.
Device farms will keep getting more sophisticated. The economics are too favorable for attackers to stop. But device intelligence shifts the advantage back to defenders by making the one thing farms cannot change, their hardware, the foundation of your fraud detection.
Frequently asked questions
What is a device farm?
How do device farms avoid detection?
What is the difference between a device farm and a bot?
How does device fingerprinting detect device farms?
Can emulators be detected?
What industries are most targeted by device farms?
Related articles

· 13 min read
Click Farm Fraud: How to Detect and Stop Fake Traffic (2026)
Click farms drain ad budgets, pollute analytics, and fake engagement. Learn how to detect and block them with device intelligence.
· 11 min read
E-Commerce Fraud Prevention at Scale: What Actually Works
57% of e-commerce traffic is bots. Platform-level fraud prevention sounds great in theory. Here is what actually works at scale.

· 11 min read
Bonus Abuse in iGaming: How It Works and How to Stop It (2026)
Bonus abuse accounts for 63.8% of iGaming fraud. Learn how fraudsters exploit promotions and how device intelligence detects them before they cash out.