E-Commerce Fraud Prevention at Scale: What Actually Works

Piero Bassa
Founder & CEO
During the 2024 holiday season, bots generated 57% of all e-commerce traffic, surpassing human visitors for the first time. Not scrapers browsing product pages. Automated tools testing stolen cards, stuffing credentials, exploiting promotions, and draining inventory during flash sales.
Meanwhile, global e-commerce fraud losses hit $48 billion in 2025, a 16% year-over-year increase. Chargebacks alone cost merchants $33.79 billion. And the hidden cost that most fraud reports miss: false declines (legitimate orders wrongly blocked by over-aggressive fraud rules) are estimated at $264 billion in lost revenue.
The standard advice is to add more tools. The average e-commerce company already uses five fraud detection systems. The result is not better protection. It is more complexity, more latency at checkout, more false positives, and more friction for real customers.
There is a better approach. It starts with understanding what has actually changed in e-commerce fraud and what the popular solutions get wrong.
The fraud landscape has shifted
E-commerce fraud is no longer primarily about stolen credit cards. The threat mix has fundamentally changed over the past two years, and most fraud prevention strategies have not kept up.
Bots are the majority of your traffic
Automated traffic surpassed human traffic across the entire internet in 2024, with 51% of all web traffic now coming from bots according to Imperva’s 2025 Bad Bot Report. In e-commerce specifically, the ratio is even more skewed.
AI-powered bots drove a 758% year-over-year increase in automated traffic to retailers during the 2025 holiday season (Kasada). These are not the crude scripts of five years ago. Modern bots use residential proxies, headless browsers, and AI to mimic human behavior convincingly enough to bypass most detection tools.
Retailers now face an average of 569,884 AI-driven attacks per day, and during peak events like Black Friday, bot traffic spikes to 30x normal levels.
Account takeover is accelerating
Account takeover (ATO) fraud losses reached $17 billion in 2025. E-commerce is the primary target, absorbing 61% of all ATO attacks according to Sift’s Q3 2025 Digital Trust Index.
The attack volume keeps climbing: ATO attempts grew 141% between H1 2021 and H1 2025 (TransUnion). The driver is straightforward. With 15 billion stolen credentials circulating on the dark web and 62% of Americans reusing passwords, credential stuffing is reliable at scale. At a 0.1-4% success rate across billions of monthly attempts, attackers compromise millions of accounts every month.
Card testing has surged
Card testing attacks increased 65% between Q2 2024 and Q2 2025 (Signifyd). Fraudsters use small transactions to verify whether stolen card numbers are active before making larger purchases. These low-value transactions often slip past payment-level fraud rules that are calibrated for bigger orders.
Friendly fraud keeps growing
Not all fraud comes from criminals. Friendly fraud (customers disputing legitimate purchases) now accounts for 61-75% of all chargebacks and grew to 36% of all reported fraud in 2024, up from 15% the year before. No amount of device intelligence or bot detection stops a real customer from filing a false dispute. But device intelligence does provide the evidence trail to fight those disputes and win.
Why “platform-level” fraud prevention falls short
A popular approach in the industry is embedding fraud detection at the platform level. The idea: if a platform like Shopify or WooCommerce integrates device intelligence into its infrastructure, all merchants on that platform benefit from shared fraud signals. A fraudulent device blocked at one merchant gets automatically flagged across every other merchant on the platform.
In theory, this sounds compelling. In practice, it has structural problems.
It depends on universal adoption
Platform-level detection only works if every merchant participates. In reality, adoption is partial. Some merchants have their own fraud tools. Others never enable optional features. The result is a fraud signal network with blind spots that attackers exploit by moving between protected and unprotected merchants.
If only 40% of merchants on a platform use the shared fraud layer, the cross-merchant visibility that makes the approach valuable covers less than half the ecosystem. Fraudsters quickly learn which merchants are protected and which are not.
Cross-merchant tracking creates GDPR liability
Under GDPR, device fingerprints constitute personal data. Sharing device fingerprints across merchants at the platform level creates a data processing chain that requires:
- Documented legal basis (legitimate interest must be balanced against user rights)
- Data Processing Agreements between the platform and every participating merchant
- Transparency to end users about cross-merchant profiling
- A Data Protection Impact Assessment for large-scale processing
France’s CNIL has already fined companies for device fingerprinting without proper consent. For platforms operating across the EU, cross-merchant device sharing is not a simple feature toggle. It is a compliance project that requires legal review, updated privacy policies, and ongoing governance.
It does not address bots
Device fingerprinting answers one question: “Have I seen this device before?” It does not answer: “Is a human behind this device?”
When 57% of e-commerce traffic is automated, identification alone is not enough. A platform that can recognize a returning device but cannot distinguish a human visitor from a headless browser running through a residential proxy has a critical detection gap.
Bot detection and device identification are complementary but distinct capabilities. Platforms that offer only identification leave merchants exposed to the largest and fastest-growing attack vector.
It adds latency at checkout
Every additional script and API call in the checkout flow costs conversion. Independent benchmarks show device fingerprinting solutions can add 300-400ms of latency per page load. At checkout, where every 100ms of delay measurably impacts conversion rates, this cost compounds across millions of transactions.
Platform-level integrations that run on every page view for every merchant multiply this latency cost across the entire ecosystem, often without merchants being able to control or optimize it.
What actually works at scale
The most effective approach to e-commerce fraud prevention does not depend on platform cooperation or cross-merchant data sharing. It works at the individual merchant level, deploys in minutes, and combines the three capabilities that actually matter.
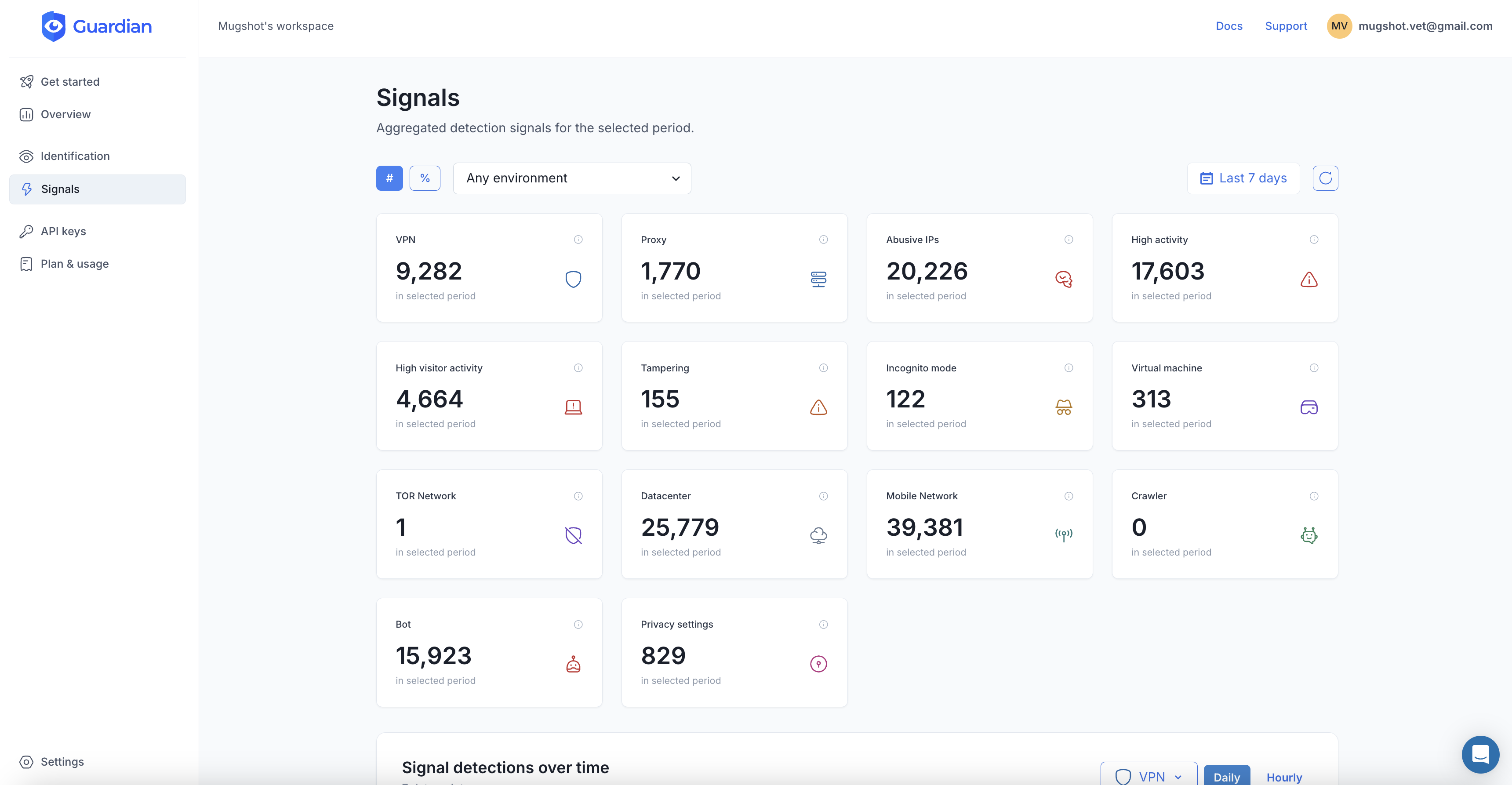
Layer 1: Persistent device intelligence
Device fingerprinting is the foundation. By combining dozens of browser, hardware, and network signals, a persistent visitor ID identifies returning visitors across sessions, even when they clear cookies, switch networks, or use incognito mode.
This layer catches the patterns that payment-level rules miss:
- Same device behind multiple accounts. One machine creating or accessing 50 “different” customer accounts is not a coincidence. It is credential stuffing or synthetic identity fraud.
- Known fraudulent devices returning. A device linked to previous chargebacks or fraud attempts should trigger elevated risk scoring on every subsequent visit, regardless of the account it logs into.
- Browser and device anomalies. Tampered user agents, spoofed screen resolutions, or mismatched timezone and language settings indicate someone trying to disguise their identity.
The key is that device intelligence must operate without collecting PII. Solutions that profile users across sites or store personal data create the same GDPR liability as cross-merchant platform approaches. The strongest solutions generate a persistent device ID from hardware and browser signals alone, with zero cookies, zero PII, and no data sent to third parties.
Layer 2: Bot detection
With the majority of e-commerce traffic now automated, bot detection is not optional. This layer identifies whether a visitor is a human or an automated tool by analyzing:
- Automation framework signals. Headless browsers (Puppeteer, Playwright, Selenium) leave detectable artifacts even when configured to mimic real browsers.
- Behavioral patterns. Bots interact with pages differently than humans. Mouse movements, scroll patterns, click timing, and navigation sequences all produce signals that machine learning models can evaluate in real time.
- Velocity anomalies. A device that initiates 200 checkout attempts in an hour or visits 500 product pages in 10 minutes is not a human shopper.
Bot detection works alongside device intelligence, not as a replacement. Device intelligence tells you which device is visiting. Bot detection tells you whether anyone is actually behind it.
Layer 3: Risk scoring per visitor
Raw signals are useful. A composite risk score per visitor is actionable. By combining device intelligence and bot detection signals into a single risk score, fraud teams can make faster and more accurate decisions:
- Low risk: Let the transaction proceed without friction. Fast checkout, happy customer.
- Medium risk: Apply additional verification. Step-up authentication, order review, or address verification.
- High risk: Block or flag the transaction. The device is known bad, the behavior is automated, or the signals do not add up.
The advantage of visitor-level risk scoring over transaction-level rules is context. A transaction that looks normal in isolation (correct card, matching billing address, typical order value) might come from a device that has been linked to 15 chargebacks in the past month. Without device-level context, that transaction sails through.
Layer 4: Payment-level rules
Device intelligence and bot detection handle the identity and intent layers. Payment-level fraud rules (Stripe Radar, Adyen risk engine, or similar) handle the transaction layer: card verification, address matching, velocity checks, and known fraud patterns in payment data.
These layers are complementary. Running payment rules without device intelligence means approving transactions from known fraudulent devices. Running device intelligence without payment rules means missing fraud signals that only surface in payment data. The strongest stacks combine both.
The privacy advantage
Privacy-first fraud prevention is not just a compliance checkbox. It is a competitive advantage that directly impacts conversion and customer trust.
No cookies means no consent banners on fraud detection
Solutions that use cookies or store PII for fraud detection trigger consent requirements under GDPR and ePrivacy. That means consent banners, user opt-outs, and reduced coverage when users decline. A solution that operates with zero cookies and zero PII runs under legitimate interest with no consent banner needed, covering 100% of visitors from the first page load.
No cross-site tracking means no regulatory risk
Cross-merchant device sharing (the “platform-level” model) requires Data Processing Agreements, impact assessments, and ongoing compliance monitoring. Merchant-level detection with no cross-site sharing avoids this entire compliance surface. There is nothing to share, nothing to govern, and nothing that regulators can question.
Customers notice
After years of cookie banners and data breach headlines, customers are increasingly wary of how their data is handled. A fraud prevention approach that adds invisible protection without collecting personal data or adding checkout friction is easier to justify to customers, to regulators, and to your own legal team.
Measuring what matters
Fraud prevention is only as good as the outcomes it produces. Track these four metrics:
Fraud rate. The percentage of transactions that are fraudulent. Industry average is around 2.9% of online transactions. If your rate is significantly higher, your detection is too permissive.
False decline rate. The percentage of legitimate orders that are wrongly blocked. This is the hidden cost most teams under-measure. False declines cost the industry $264 billion in lost revenue annually. If your fraud rate is low but your approval rate is also low, you are blocking real customers.
Checkout latency impact. Measure the page load time difference with and without your fraud detection scripts. Every 100ms matters at checkout. If your fraud prevention adds more than 100ms, evaluate whether that cost is justified by the detection quality it provides.
Chargeback ratio. Card networks impose penalties when chargeback rates exceed thresholds (typically 0.9-1% of transactions). Staying well below these thresholds protects your merchant account and processing fees.
The bottom line
E-commerce fraud prevention at scale does not require a platform-level integration that takes months to deploy, creates privacy liability, and still misses the 57% of traffic that is automated.
It requires device intelligence that works without PII, bot detection that catches what network-layer tools miss, and risk scoring that gives fraud teams clear, actionable signals on every visitor.
The strongest approach is merchant-level, privacy-first, and fast to deploy. A single script tag, under 15 minutes to production, covering login, checkout, and account management flows with zero cookies, zero PII, and no third-party data sharing.
The fraud is already here. The bots are already the majority of your traffic. The question is whether your detection can keep up without slowing down the customers who actually want to buy.
Frequently asked questions
What is the best approach to e-commerce fraud prevention at scale?
Does device fingerprinting violate GDPR?
How much does e-commerce fraud cost merchants?
Can bots bypass device fingerprinting?
Related articles

· 13 min read
Click Farm Fraud: How to Detect and Stop Fake Traffic (2026)
Click farms drain ad budgets, pollute analytics, and fake engagement. Learn how to detect and block them with device intelligence.

· 13 min read
Device Farm Fraud: How to Detect and Shut Down Fake Traffic
Device farms power fake accounts, promotion abuse, and credential stuffing at scale. Learn how device intelligence detects and stops them.
· 11 min read
The 10 Best E-Commerce Fraud Prevention Tools in 2026
Compare the 10 best e-commerce fraud prevention tools for 2026. Features, pricing, and how to choose the right solution for your store.