Multi-Accounting in Online Gambling: How to Detect and Stop It

Piero Bassa
Founder & CEO

In February 2026, federal prosecutors in Connecticut indicted two 29-year-old men for using approximately 3,000 stolen identities to create fake accounts on FanDuel and other gambling platforms. The scheme ran for five years, generated $3 million in fraudulent profits, and went undetected until a joint investigation by the IRS and state gaming regulators pieced together the operation. The pair bought personal data on the darknet, passed identity verification checks, claimed promotional bonuses on every fake account, and funneled winnings through virtual stored-value cards into personal bank accounts.
Their operation was sophisticated but not unique. Multi-accounting is the most common fraud vector in online gambling, and 82.9% of operators say the problem is getting worse. First-party fraud cost gaming operators $2.8 billion in 2024 alone, according to Socure. The global online gambling market now exceeds $117 billion, and every operator offering sign-up bonuses, free bets, or loyalty rewards is a target.
Here is how multi-accounting works, why standard defenses fail, and what actually stops it.
What multi-accounting looks like in practice
Multi-accounting is exactly what it sounds like: one person operating multiple accounts on the same platform. Every major gambling operator prohibits it, but enforcement is the hard part. The technique enables nearly every other fraud type in the industry.
Bonus abuse
This is the primary motivation. Bonus abuse accounts for 63.8% of all fraud in the iGaming sector, according to Sumsub’s 2025 report. Fraudsters create dozens or hundreds of accounts to claim welcome bonuses, free spins, deposit matches, and promotional free bets. Each account looks like a new customer. Each one claims a first-time bonus that the operator funds from their marketing budget.
The economics are staggering. Sumsub estimates that an inexperienced bonus abuser can make up to $20,000 per month. A skilled operator running hundreds of accounts can earn up to $600,000 monthly. Operators lose approximately 15% of their promotional budgets to these schemes.
Gnoming
Gnoming is multi-accounting using someone else’s identity. When a bettor gets banned or restricted (“gubbed”) by a platform, they recruit friends, family members, or paid accomplices to share their personal details: ID cards, proof of address, utility bills, banking information. The banned player then opens and operates accounts under these identities.
This is particularly common in matched betting circles and among players who have been limited by sportsbooks for winning too consistently. The accounts appear legitimate because they belong to real people with genuine documents, making them extremely difficult to detect through KYC alone.
Arbitrage betting
Multi-accounting amplifies arbitrage by letting fraudsters place opposing bets across multiple accounts on the same platform. They exploit temporary odds discrepancies to guarantee profit regardless of the outcome. With enough accounts, even small distortions yield consistent returns.
Indicators include accounts that consistently bet on specific odds differences, place stakes within seconds of odds changes, and use welcome bonuses strategically to maximize returns on arbitrage positions.
Poker collusion and chip dumping
In online poker, multi-accounting lets a single player control multiple seats at the same table. This provides a massive mathematical advantage: seeing more hole cards means better decision-making at every stage. Coordinated accounts can raise and fold strategically to trap opponents, extract maximum value from pots, and dump chips between accounts.
Chip dumping, where one account deliberately loses to another, is also used for money laundering. Illicit funds deposited into one account can be “lost” to a clean account at the poker table, creating a seemingly legitimate source of winnings.
Self-exclusion bypass
This is where multi-accounting becomes a player protection issue, not just a revenue issue. Problem gamblers who self-exclude from platforms can create new accounts with different email addresses, slightly altered names, or borrowed identities. A 2019 UK investigation found that players could bypass self-exclusion by simply changing their email address.
Regulators are increasingly holding operators responsible for detecting these cases. Under UKGC rules, operators must verify identity before any gambling activity, and failing to prevent self-exclusion bypass carries significant penalties.
The scale of the problem
The numbers make the urgency clear.
iGaming fraud increased 64% year-over-year between 2022 and 2024, according to Sumsub. The top three threats cited by operators are identity fraud (64.8%), money laundering (64.8%), and bonus abuse (63.8%). These categories overlap heavily, and multi-accounting is the common thread.
A third of operators estimate fraud costs them 10-20% of annual revenue. For a mid-sized operator generating $100 million annually, that is $10-20 million lost to fraud. In the first half of 2025 alone, the global casino industry paid $160.3 million in regulatory fines across 40+ enforcement actions in eight countries.
The FanDuel case is one example among thousands. Organized fraud rings operate globally, using stolen identities, synthetic documents, and automated tools to create accounts at scale. The barrier to entry is low: anti-detect browsers cost $50-100 per month, stolen identity data is readily available on the darknet and Telegram, and a single operator can manage hundreds of accounts from one workstation.
Why traditional defenses fail
Most gambling platforms rely on a combination of KYC verification, IP tracking, and email/phone verification. Each of these has critical blind spots.
KYC verification
KYC is a compliance requirement, not a fraud detection tool. Sumsub reports that 76% of fraud attempts occur after KYC is completed. The reason is straightforward: fraudsters use identities that pass verification.
Stolen identities come with real documents. Synthetic identities combine real data fragments (a valid Social Security number, a genuine address) with fabricated details. Deepfake technology now bypasses selfie-based liveness checks. Deepfake fraud grew 700% between Q1 2024 and Q1 2025, and humans correctly identify high-quality deepfakes only 24.5% of the time.
KYC tells you who someone claims to be. It does not tell you whether the person behind the screen is the same person on the document, or whether they already have five other accounts.
IP address tracking
Flagging multiple accounts from the same IP address was effective a decade ago. It is not effective now. VPNs, residential proxies, and mobile data connections make IP-based detection trivial to bypass.
An estimated 1.75 billion people worldwide use VPNs. Residential proxy services route traffic through real home internet connections, making fraudulent traffic indistinguishable from legitimate users by IP alone. A multi-accounting operation can assign a different residential IP to every single account.
Email and phone verification
Disposable email services generate unlimited unique addresses. Virtual phone number services provide SMS verification for pennies per number. These are not barriers to fraud; they are minor costs of doing business for organized operations.
CAPTCHAs
CAPTCHAs add friction for legitimate users without stopping determined fraudsters. Solving services handle CAPTCHAs at $1-3 per thousand challenges. Multi-accounting operations budget for this as an operating expense, not an obstacle.
Behavioral rules
Simple rules like “flag accounts that bet the same amount on the same event” catch only the most careless fraudsters. Sophisticated operators vary their behavior across accounts: different bet sizes, different sports, different session times. They know what patterns platforms look for and deliberately avoid them.
What actually works: layered device intelligence
The fundamental weakness of identity-based and network-based detection is that both can be faked. Identities can be stolen or synthesized. IP addresses can be proxied. Emails and phone numbers can be generated on demand.
What cannot be faked at scale is the physical device behind the session.
Device fingerprinting
Device fingerprinting collects signals from the hardware and software stack of every visitor: GPU renderer, canvas rendering output, audio processing characteristics, screen properties, installed fonts, browser configuration, and dozens more. These signals combine into a fingerprint that identifies the physical device with over 99% accuracy.
When a fraudster creates account number 47 on the same laptop and browser, the fingerprint matches accounts 1 through 46, even if every other signal (IP, email, name, documents) is different. Clearing cookies and using incognito mode do not change the underlying hardware signals. Switching browsers or a major browser update can produce a new fingerprint, but platforms that store historical fingerprints per account can still cluster these identifiers together, building a complete picture of device reuse across accounts.
Tamper and spoofing detection
Anti-detect browsers like Multilogin and GoLogin attempt to spoof device fingerprints by randomizing browser parameters. Over 24 anti-detect browsers now exist in the market, and gambling is one of their most common use cases.
Advanced device intelligence detects these tools by identifying inconsistencies between claimed and actual hardware characteristics. A browser claiming to run on an iPhone but rendering WebGL like a desktop GPU reveals the spoofing attempt. Guardian’s tampering detection flags these inconsistencies with a confidence score.
Velocity and behavioral signals
Device intelligence tracks how many accounts, sessions, and events originate from a single device over time. A legitimate user creates one account. A fraudster creates dozens. Velocity signals catch this pattern regardless of how carefully the fraudster varies their behavior on each account.
Timing patterns also reveal fraud. Sumsub reports that most fraudulent activity occurs between 4-8 a.m., while legitimate players register around 6 p.m. Fraud operations run on schedules optimized for when compliance teams are offline.
VPN and proxy detection
Device intelligence layers include VPN and proxy detection that identifies when traffic is routed through anonymizing services. While a VPN is not proof of fraud, it is a risk signal. When combined with other indicators (new account, large bonus claim, browser tampering), it helps build a complete risk profile.
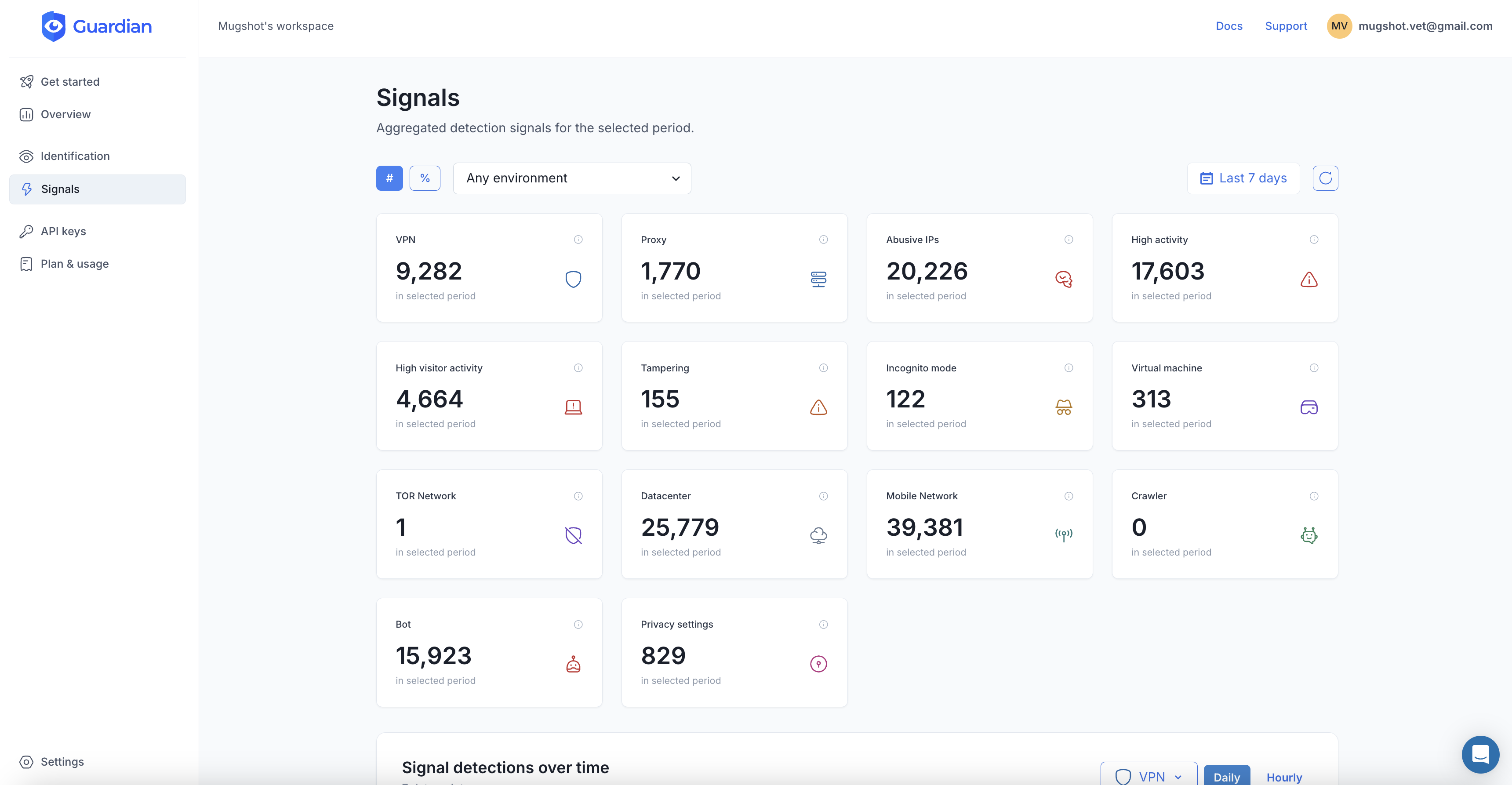
Detecting multi-accounting with Guardian
Guardian combines 70+ device and browser signals with server-side analysis to identify every visitor to your gambling platform. Its persistent device fingerprinting recognizes returning devices across sessions, incognito mode, and cookie clears.
Here is how to integrate it into a gambling platform’s account creation and login flow.
1. Install the JavaScript agent
import { loadAgent } from '@guardianstack/guardian-js';
const guardian = await loadAgent({
siteKey: 'YOUR_SITE_KEY',
});
const { requestId } = await guardian.get();
// Send requestId to your server with the registration or login request2. Check device signals on the server
import {
createGuardianClient,
isBot,
isTampering,
isVPN,
} from '@guardianstack/guardianjs-server';
const client = createGuardianClient({
secret: process.env.GUARDIAN_SECRET_KEY,
});
const event = await client.getEvent(requestId);
// Check if the device has been seen on other accounts
const { visitorId } = event;
const existingAccounts = await db.query(
'SELECT account_id FROM accounts WHERE visitor_id = $1',
[visitorId]
);
if (existingAccounts.length > 0) {
// This device is linked to existing accounts - flag for review
await flagMultiAccounting(visitorId, existingAccounts);
}3. Use Smart Signals for risk assessment
Guardian’s response includes signals specifically relevant to gambling fraud:
{
"visitorId": "abc123def456",
"browserTampering": {
"detected": true,
"score": 0.92,
"anomalies": ["canvas_mismatch", "webgl_spoofing"]
},
"vpnDetection": {
"detected": true,
"provider": "residential_proxy"
},
"velocity": {
"5m": 1,
"1h": 4,
"24h": 23
},
"virtualization": {
"detected": false
}
}A device with browser tampering detected, a residential proxy connection, and 23 events in 24 hours is almost certainly part of a multi-accounting operation. Your platform can automatically block registration, require enhanced verification, or flag the account for manual review.
4. Map devices to accounts
The most powerful pattern is maintaining a device-to-account mapping. Every time a user registers or logs in, store the visitorId alongside their account ID. A single account may accumulate a few identifiers over time (different browsers, major updates), so store all of them rather than overwriting. Over time, this builds a graph of which devices access which accounts.
A legitimate user has a handful of identifiers linked to one account. A multi-accounting operation has the same identifier (or a small cluster of them from the same machine) linked to dozens of accounts. This signal is unambiguous and extremely difficult to fake.
Building a multi-accounting defense strategy
Device intelligence is the core layer, but effective defense requires a stack.
-
Collect device signals at registration. Fingerprint every device that creates an account. Store the visitor ID and check it against existing accounts before approving the registration.
-
Layer KYC as a compliance check, not a fraud check. KYC satisfies regulatory requirements (UKGC, MGA, Curacao) but should not be your primary fraud detection mechanism. Use it alongside, not instead of, device intelligence.
-
Monitor post-registration behavior. Sumsub reports that 41.9% of fraud attempts occur at the deposit stage, not at registration. Continue checking device signals on deposits, withdrawals, and bonus claims.
-
Flag, do not just block. Not every multi-device signal is fraud. Shared household devices, workplace computers, and phone upgrades create legitimate multi-account signals. Use risk scoring to prioritize manual review rather than automated blocking.
-
Enforce self-exclusion with device matching. When a player self-excludes, store their device fingerprint. If a new account appears from the same device, flag it for review regardless of the identity used. This turns device intelligence into a responsible gambling tool.
-
Report and adapt. Track fraud patterns over time. Multi-accounting techniques evolve: new anti-detect browsers appear, new proxy services launch, and fraudsters share evasion techniques. Regular analysis of blocked attempts reveals emerging tactics.
The regulatory dimension
Regulators are tightening requirements around fraud detection and player protection, making multi-accounting prevention not just a revenue issue but a compliance obligation.
The UKGC launched a new financial penalties framework in October 2025, with the most serious breaches carrying fines of 15% of gross gambling yield or more. Platinum Gaming (Unibet’s operator) received a GBP 10 million fine for AML and responsible gambling failures. Spain imposed nearly EUR 111 million in gambling penalties across 58 sanctions in 2025.
Curacao completed its gaming reform in 2025, replacing the old sub-licensing system with a single Curacao Gaming Authority. From January 2026, all licensees must maintain physical offices in Curacao and implement robust KYC, AML, and player protection systems.
The direction is clear: regulators expect operators to detect and prevent multi-accounting. Operators who rely solely on KYC are falling behind both the fraudsters and the regulators.
The cost of inaction
The math is simple. A mid-sized gambling operator losing 10-20% of revenue to fraud is bleeding $10-20 million per year. The FanDuel case shows that even a two-person operation can extract $3 million over five years. Organized rings operating at scale extract far more.
Device intelligence is not free, but the return is immediate. Blocking even a fraction of multi-accounting activity pays for the investment many times over, while simultaneously improving regulatory compliance and protecting vulnerable players from self-exclusion bypass.
Start your free trial to see how Guardian detects multi-accounting on your gambling platform.
Frequently asked questions
What is multi-accounting in online gambling?
How do fraudsters create multiple gambling accounts?
How much does multi-accounting fraud cost gambling operators?
Can KYC verification stop multi-accounting?
How does device fingerprinting detect multi-accounting?
What is gnoming in gambling?
Related articles

· 11 min read
Bonus Abuse in iGaming: How It Works and How to Stop It (2026)
Bonus abuse accounts for 63.8% of iGaming fraud. Learn how fraudsters exploit promotions and how device intelligence detects them before they cash out.

· 13 min read
Click Farm Fraud: How to Detect and Stop Fake Traffic (2026)
Click farms drain ad budgets, pollute analytics, and fake engagement. Learn how to detect and block them with device intelligence.

· 13 min read
Device Farm Fraud: How to Detect and Shut Down Fake Traffic
Device farms power fake accounts, promotion abuse, and credential stuffing at scale. Learn how device intelligence detects and stops them.