NIS2 Directive Explained: Requirements, Penalties, Deadlines

Piero Bassa
Founder & CEO

The EU’s original cybersecurity directive covered a few thousand companies across roughly seven sectors. Its replacement, NIS2, covers 160,000 entities across 18 sectors. If your business operates in Europe and touches anything from cloud infrastructure to food production, you are likely in scope.
NIS2 is not a suggestion. It is a binding EU directive with penalties that rival GDPR, personal liability for executives, and a 24-hour incident reporting window that makes “we didn’t know” an unacceptable answer. Here is everything you need to understand about it.
What is the NIS2 directive?
NIS2 (Directive EU 2022/2555) is the EU’s updated framework for cybersecurity across critical and important sectors. Adopted in December 2022, it replaces the original NIS Directive from 2016 and introduces significantly broader scope, stricter requirements, and harmonized enforcement across all 27 EU member states.
The core goal is straightforward: raise the baseline level of cybersecurity across the EU by requiring organizations to actively manage cyber risks, report incidents quickly, and prove they are doing both.
Where NIS1 left most decisions to individual member states (leading to wildly inconsistent implementation), NIS2 imposes uniform rules. Every covered entity in every member state must meet the same standards, face the same penalties, and follow the same reporting timelines.
Who must comply: essential vs important entities
NIS2 introduces a clear size-cap rule that eliminates the guesswork of NIS1’s country-by-country identification.
Essential entities are large companies in high-criticality sectors:
- 250+ employees, or
- EUR 50M+ annual turnover, or
- EUR 43M+ balance sheet total
Important entities are medium companies in the same or additional sectors:
- 50+ employees, or
- EUR 10M+ annual turnover, or
- EUR 10M+ balance sheet total
Some entities are in scope regardless of size. DNS service providers, TLD name registries, trust service providers, public electronic communications networks, and central government bodies all fall under NIS2 no matter how small they are.
Both categories must implement identical security measures under Article 21. The difference lies in how they are supervised and what they pay when things go wrong.
| Essential entities | Important entities | |
|---|---|---|
| Supervision | Proactive (audits, inspections anytime) | Reactive (only after evidence of non-compliance) |
| Max fine | EUR 10M or 2% global turnover | EUR 7M or 1.4% global turnover |
| Management bans | Yes (temporary, for repeat violations) | No |
| Security requirements | Article 21 (all 10 measures) | Article 21 (all 10 measures) |
| Incident reporting | 24h / 72h / 1 month | 24h / 72h / 1 month |
The 18 sectors covered by NIS2
NIS2 splits coverage into two annexes. Annex I lists sectors of high criticality (primarily essential entities). Annex II lists other critical sectors (primarily important entities).
Annex I: high criticality
- Energy (electricity, oil, gas, hydrogen, district heating)
- Transport (air, rail, water, road)
- Banking (credit institutions)
- Financial market infrastructures (trading venues, central counterparties)
- Health (hospitals, pharmaceutical manufacturers, medical device makers)
- Drinking water (suppliers and distributors)
- Wastewater (treatment operators)
- Digital infrastructure (cloud providers, data centers, CDNs, DNS providers, IXPs, telecom operators)
- ICT service management (managed service providers, managed security service providers)
- Public administration (central and regional government)
- Space (ground-based infrastructure operators)
Annex II: other critical sectors
- Postal and courier services
- Waste management
- Chemical manufacturing and distribution
- Food production and distribution (wholesale, industrial processing)
- Manufacturing (medical devices, electronics, electrical equipment, machinery, motor vehicles, other transport equipment)
- Digital providers (online marketplaces, search engines, social networks)
- Research organizations
If your company falls into any of these sectors and meets the size thresholds, you are in scope. There is no opt-out and no exemption for “we’re just a software company.”
The 10 required security measures under Article 21
Article 21 is the technical heart of NIS2. It mandates 10 categories of cybersecurity risk-management measures that every covered entity must implement. These are technology-neutral and outcomes-based, meaning NIS2 does not prescribe specific tools. It prescribes results you must demonstrate.
1. Risk analysis and information system security policies
You need formal, documented risk assessments covering your IT and OT infrastructure. This means identifying threats, vulnerabilities, and attack likelihood for every system that supports your operations.
For web-facing businesses, this includes assessing the risk from automated traffic. Bot attacks account for over half of all internet traffic, and they target login pages, APIs, and checkout flows directly. A risk analysis that ignores automated threats is incomplete.
2. Incident handling
Procedures for prevention, detection, analysis, containment, response, and recovery. You need to know when an incident happens, classify its severity, contain it, and document everything.
This is where visibility matters most. If a credential stuffing campaign compromises accounts at 2am, you need systems that detect it in real time, not in a weekly log review.
3. Business continuity and disaster recovery
Plans for maintaining operations during major cyber incidents. This includes verified backup procedures, defined system restoration sequences, and crisis communication protocols.
4. Supply chain security
You must assess and manage cyber risks across your entire value chain. That means evaluating direct suppliers’ cybersecurity posture and including security requirements in contracts.
This requirement cuts both ways. If your customers are NIS2-regulated, they will require you to prove your security measures. A logistics platform serving energy companies, a SaaS tool used by hospitals, an analytics provider embedded in banking infrastructure: all will face contractual pressure to demonstrate NIS2-level security.
5. Security in system acquisition, development, and maintenance
Secure development lifecycle practices, vulnerability handling, and disclosure procedures. If you build software, your development process must account for security from design through deployment.
6. Effectiveness assessment
Policies and procedures to regularly test, audit, and review your security controls. This is not a one-time checkbox. NIS2 requires ongoing proof that your measures actually work.
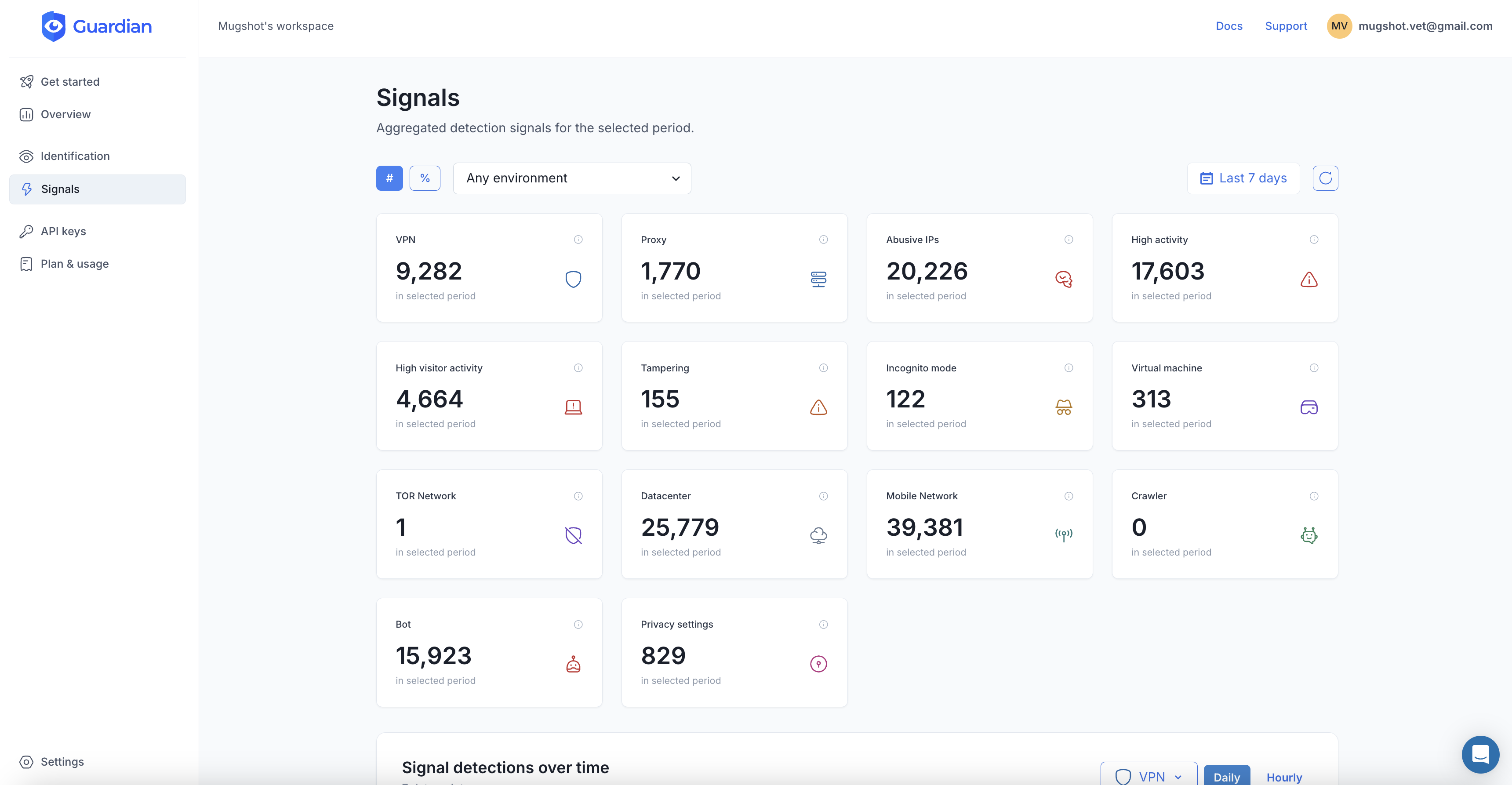
Continuous monitoring dashboards, automated threat detection analytics, and regular penetration testing all serve this requirement. The key word is “ongoing.” Auditors will ask for evidence of continuous assessment, not an annual report.
7. Cybersecurity training and basic cyber hygiene
Staff awareness programs, phishing simulations, and security culture building. Every employee must understand their role in preventing incidents.
8. Cryptography and encryption policies
Documented standards for data-at-rest and data-in-transit encryption. Where appropriate, encryption must be applied to protect sensitive information.
9. Access control and asset management
Role-based access control, principle of least privilege, personnel vetting, and asset inventory. You need to know what devices are accessing your systems and whether they should be.
This is where device intelligence becomes directly relevant. Knowing that a login request comes from a recognized, trusted device versus a spoofed environment or a device farm is exactly the kind of asset-level visibility NIS2 demands. It is not enough to verify credentials. You must verify the device itself.
10. Multi-factor authentication and continuous authentication
MFA or continuous authentication solutions, secured communications, and emergency communication systems. The directive explicitly calls for authentication that goes beyond passwords.
Device fingerprinting functions as a continuous, invisible authentication layer. It does not replace MFA, but it strengthens it by verifying that the device presenting credentials is trusted, not just the credentials themselves. When a login comes from a known device with a consistent fingerprint, that is a strong authentication signal. When it comes from a residential proxy on a spoofed browser, that is a risk signal, and exactly the kind of evidence NIS2 expects you to act on.
Incident reporting: the 24-72-30 timeline
NIS2 replaces the vague “without undue delay” language of NIS1 with a strict three-stage reporting framework.
Stage 1: early warning (within 24 hours). As soon as you become aware of a significant incident, you must notify your national CSIRT or competent authority. This initial report must indicate whether the incident appears to be caused by unlawful or malicious acts and whether it could have cross-border impact.
Stage 2: incident notification (within 72 hours). An updated report with your initial assessment of the incident, its severity, its impact, and any indicators of compromise you have identified.
Stage 3: final report (within 1 month). A detailed description of the incident including the root cause, all mitigation measures applied, and the cross-border impact if applicable.
What qualifies as a “significant incident”
An incident is significant if it has caused or could cause severe operational disruption, financial loss, or considerable damage to other persons. For web-facing businesses, this includes:
- Credential stuffing campaigns that compromise user accounts at scale
- DDoS attacks that degrade service availability
- Data scraping that exposes personal or proprietary information
- Payment fraud driven by automated bots
- Account takeover that affects multiple users
The 24-hour clock starts when you become “aware” of the incident. If your detection systems are slow or nonexistent, awareness may come from your customers, the press, or your regulator. None of those are good options.
Penalties and management liability
Financial penalties
For essential entities: up to EUR 10,000,000 or 2% of total worldwide annual turnover, whichever is higher.
For important entities: up to EUR 7,000,000 or 1.4% of total worldwide annual turnover, whichever is higher.
These are calculated on global revenue, not just EU operations. A US-based SaaS company with EUR 500M in worldwide revenue serving EU customers as a digital infrastructure provider faces a potential EUR 10M fine, even if only a fraction of that revenue comes from the EU.
Personal liability for executives
This is where NIS2 fundamentally changes the game. Article 20 requires management bodies to:
- Approve cybersecurity risk-management measures
- Oversee their implementation
- Complete cybersecurity training to acquire sufficient knowledge for evaluating risks
Management body members can be held personally liable if gross negligence is proven after a cyber incident. For essential entities, authorities can impose a temporary ban on individuals holding management positions in cases of repeated violations.
The board cannot simply delegate cybersecurity to the CISO and walk away. NIS2 requires documented evidence that leadership actively participated: board meeting minutes discussing cyber risks, training certificates, formal approval of security policies.
What this means for web-facing businesses
If your business runs web applications, APIs, or customer-facing portals, NIS2’s requirements map directly to threats you are already dealing with (or should be).
The directive does not name specific technologies. It describes outcomes you must achieve: risk analysis, incident detection, access control, continuous authentication, effectiveness assessment. For any company where users interact through a browser or mobile app, meeting those outcomes requires visibility into who and what is accessing your systems.
You cannot assess risk you cannot see. Article 21(a) requires risk analysis. If 40% of your traffic is automated and you do not know it, your risk analysis has a blind spot the size of your entire threat surface.
You cannot report incidents you do not detect. Article 23 requires a 24-hour early warning. If a bot attack compromises thousands of accounts overnight and you find out from a customer complaint three days later, you have already missed the reporting window.
You cannot prove access control without device-level visibility. Article 21(i) requires knowing what is accessing your systems. Device fingerprinting provides exactly this: persistent identification of every device that touches your application, with risk scoring that distinguishes trusted devices from spoofed environments, emulators, and automation frameworks.
You cannot claim continuous authentication without continuous signals. Article 21(j) explicitly calls for continuous authentication solutions. Device intelligence provides a passive, invisible authentication layer that evaluates trust on every interaction, not just at login. That is continuous authentication in practice, and it produces the auditable evidence NIS2 requires.
This is where Guardian fits. Guardian’s device intelligence provides device-level risk scoring on every session, bot detection that identifies automated threats before they become incidents, and visitor identification that gives you persistent device-level visibility across sessions. That is not a compliance pitch. That is the practical tooling you need to produce the evidence NIS2 auditors will ask for.
Key deadlines and transposition status
NIS2 entered into force on January 16, 2023. The transposition deadline for member states was October 17, 2024. Here is where things stand as of early 2026.
Countries that have transposed
Belgium, Croatia, Denmark, Estonia, Finland, Germany, Greece, Hungary, Italy, Latvia, Lithuania, Malta, Romania, Slovakia, and Slovenia have all completed their national transposition. Germany’s NIS2UmsuCG took effect in December 2025 with registration opening in January 2026, pulling an estimated 29,500 entities into scope (up from 4,500 under NIS1).
Countries still finalizing
France, the Netherlands, Spain, Poland, Austria, Portugal, Ireland, and Sweden are in various stages of completing their legislation. France’s Senate approved its bill in March 2025, with the National Assembly process continuing into 2026. The Netherlands expects its cybersecurity bill to take effect in Q2 2026.
What comes next
- Mid-2026: First NIS2 audits expected in countries that have transposed
- October 2027: European Commission reviews the directive’s functioning
- Ongoing: The Commission’s infringement proceedings against late-transposing states continue, with possible referrals to the Court of Justice
The window for “wait and see” has closed. If you operate in a covered sector and meet the size thresholds, compliance is not a future obligation. It is a current one, and the audit machinery is starting to move.
NIS2 and related EU regulations
NIS2 does not exist in isolation. It sits alongside several other EU frameworks, and understanding the overlaps is critical for efficient compliance.
GDPR protects personal data. NIS2 protects network and information systems. When a cybersecurity incident involves personal data (which most do), you must file parallel notifications under both frameworks.
DORA (Digital Operational Resilience Act) is the sector-specific law for financial entities. Banks, insurance companies, investment firms, and crypto-asset service providers fall under DORA instead of NIS2 to avoid duplication.
CRA (Cyber Resilience Act) focuses on products with digital elements, requiring security-by-design. CRA ensures products entering the EU market are secure. NIS2 ensures organizations using those products maintain ongoing security. Full CRA application begins December 2027.
The common thread across all of these: the EU is building a layered regulatory framework where cybersecurity is no longer optional, no longer a suggestion, and no longer just an IT concern. It is a board-level, legally binding obligation with teeth.
If you are in scope, the time to build your compliance posture is now. Start with visibility into what is actually hitting your systems. Everything else follows from there.
Frequently asked questions
Does NIS2 apply to companies outside the EU?
What is the difference between essential and important entities under NIS2?
What happens if you don't comply with NIS2?
How is NIS2 different from GDPR?
Does NIS2 require bot detection?
Related articles

· 12 min read
NIS2 Compliance Checklist: 10 Measures You Need in 2026
A practical NIS2 compliance checklist mapping Article 21's 10 cybersecurity measures to concrete actions. Includes audit preparation and reporting timelines.
· 11 min read
NIS2 for SaaS Companies: Who's in Scope and How to Comply
SaaS companies with 50+ employees or EUR 10M+ revenue are in NIS2's scope. Learn what's required, which sectors are affected, and how to prepare.

· 11 min read
Deepfakes vs. Gambling KYC: Why Identity Checks Are Failing
Deepfake fraud in gambling grew 700% in one year. Learn why KYC alone cannot stop identity fraud and how device intelligence fills the gap.